
The Cuba ransomware gang was observed in attacks targeting critical infrastructure organizations in the United States and IT firms in Latin America, using a combination of old and new tools.
BlackBerry's Threat Research and Intelligence team, which spotted the latest campaign in early June 2023, reports that Cuba now leverages CVE-2023-27532 to steal credentials from configuration files.
The particular flaw impacts Veeam Backup & Replication (VBR) products, and an exploit for it has been available since March 2023.
Previously, WithSecure reported that FIN7, a group with multiple confirmed affiliations with various ransomware operations, was actively exploiting CVE-2023-27532.
Cuba attack details
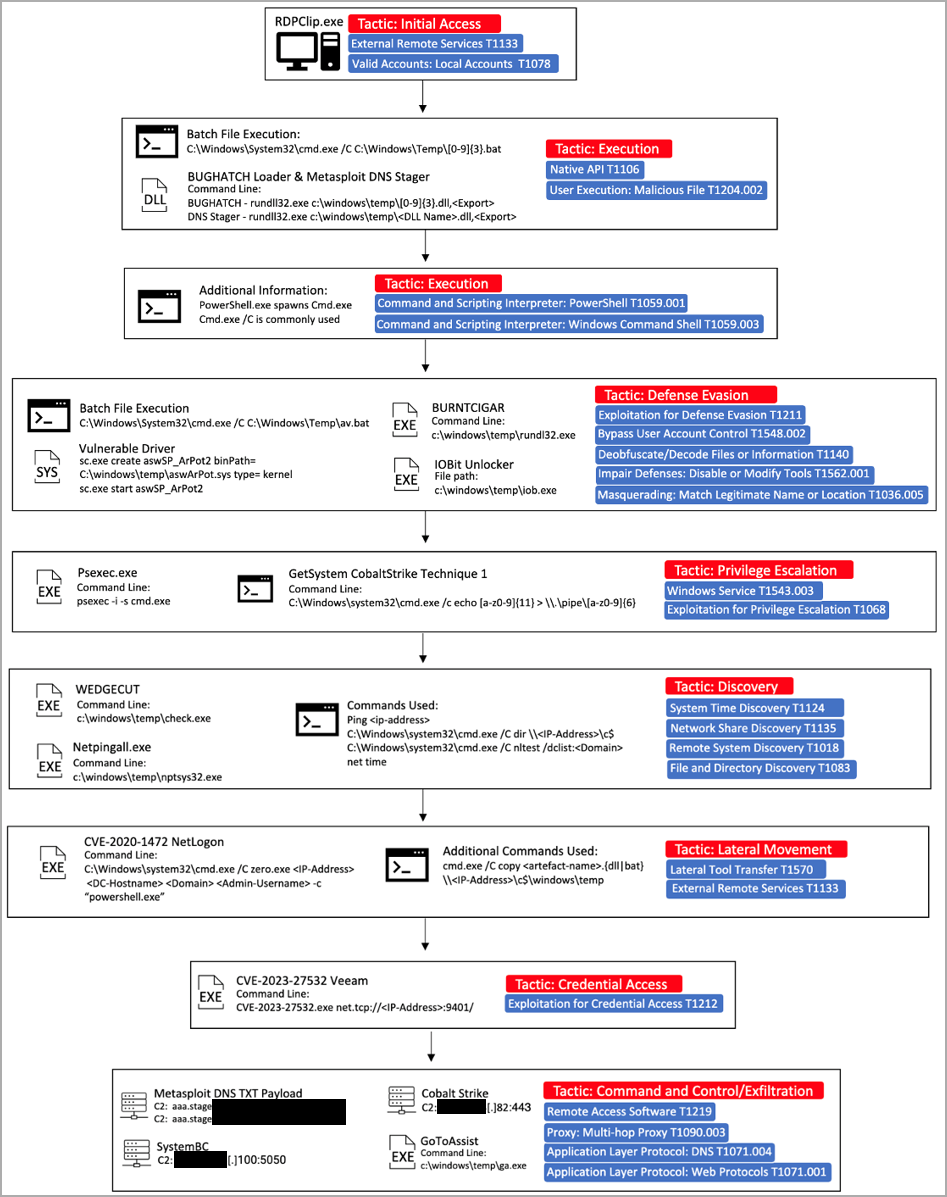
BlackBerry reports that Cuba's initial access vector appears to be compromised admin credentials via RDP, not involving brute forcing.
Next, Cuba's signature custom downloader 'BugHatch' establishes communication with the C2 server and downloads DLL files or executes commands.
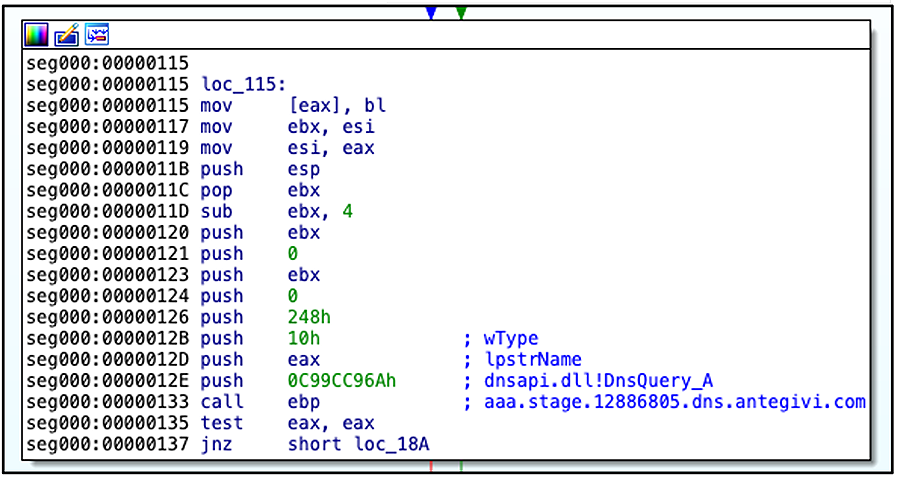
An initial foothold on the target environment is achieved through a Metasploit DNS stager that decrypts and runs shellcode directly in memory.
Cuba utilizes the now-widespread BYOVD (Bring Your Own Vulnerable Driver) technique to turn off endpoint protection tools. Also, it uses the 'BurntCigar' tool to terminate kernel processes associated with security products.
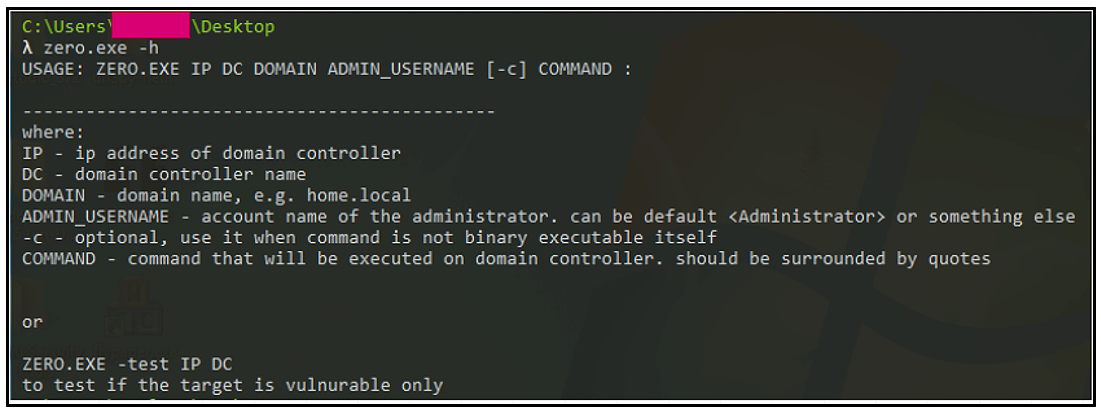
Apart from the Veeam flaw that's relatively recent, Cuba also exploits CVE-2020-1472 ("Zerologon"), a vulnerability in Microsoft's NetLogon protocol, which gives them privilege escalation against AD domain controllers.
In the post-exploitation phase, Cuba was observed using Cobalt Strike beacons and various "lolbins."
Cuba still very active
BlackBerry underlines the clear financial motivation of the Cuba ransomware gang and mentions that the threat group is likely Russian, something that has been hypothesized by other cyber-intelligence reports in the past.
This assumption is based on the exclusion of computers that use a Russian keyboard layout from infections, Russian 404 pages on parts of its infrastructure, linguistic clues, and the group's Western-focused targeting.
In conclusion, Cuba ransomware remains an active threat approximately four years into its existence, which isn't common in ransomware.
The inclusion of CVE-2023-27532 in Cuba's targeting scope makes the prompt installation of Veeam security updates extremely important and once again highlights the risk of delaying updates when publicly available PoC (proof-of-concept) exploits are available.


Comments
whentechnologyfails - 10 months ago
They should rather export Coffee and make their fortune that way. Dictatorships are like the Daycare.
Full of toddlers.